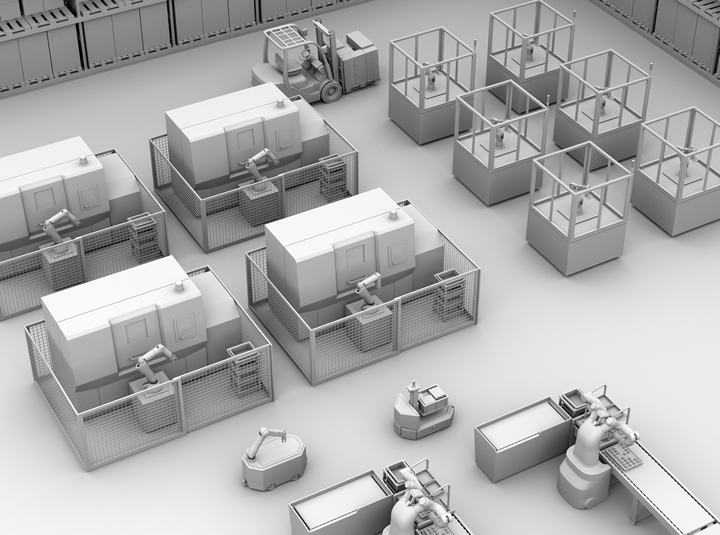
Industrial Robots Are at Increased Risk of Cybersecurity Threats: 7 Considerations for 2024
Industrial robot adoption is reaching new heights as manufacturers embrace Industry 4.0 initiatives. As beneficial as this movement is, it has led to some unexpected challenges for the sector. Most notably, robots are becoming a common target for cyberattacks.
10 Factors Warehouse Managers Should Consider for Goods-to-Person Fulfilment
In this article, let's dive deeper into how it works and what factors you should consider if you are thinking to switch to using the Goods-to-Person fulfillment model.
Access Control Key to Cybersecurity in B2B eCommerce
Using Access Control Lists (ACLs) to establish rules that grant or deny access to different data types includes sensitive data. Every user in an application has a role, and every role has a set of permissions configured to perform or restrict actions to entities and system capabilities.
What Security Privileges Should We Give to AI?
In a survey, some 80% of telecommunications executives stated they believe their organization cannot respond appropriately to cyberattacks without AI. What's more, 69% of all senior executives agree they would not be able to respond without AI on their side.
Could Your Robot Be Spying on You? - Cybersecurity Tips for Manufacturers Employing Robotics
Whether it is smart phone manufacturing, car-making or the food and beverage sector, factories around the world are already equipped with robots and other automated technologies. So how much of a threat is the possibility of these robots being hacked?
Ways to Optimize Manufacturing Cybersecurity
Manufacturing facilities are at an increasingly high risk of cyberattacks, especially as they feature more connected, advanced machines that play vital roles in operations.
Surviving a Global Cyberattack - Company Culture Plays a Pivotal Role
Pilz was hit with a ransomware cyberattack on October 13, 2019. In the following article, written by Mike Beerman, CEO, Pilz USA, discusses how Pilz not only survived the attack, but is coming back stronger than ever.
Robot Network Security
RAD solutions are used in a variety of markets for critical infrastructure like corporate headquarters, healthcare campuses, higher education campuses, event venues and government facilities.
Securing The Robots
There is no magic bullet for robot security. They are simply devices executing code, which are just as likely to be compromised as any other device in an organisation.
Report: Cyberattacks on Industrial Robots
Trend Micro recently released the first in-depth, hands-on research that demonstrates the extent to which industrial robots can be compromised.
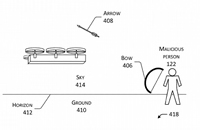
Amazon patents system to defend drones against hackers, jammers "¦ and arrows
Alan Boyle for GeekWire: If there are any Robin Hoods out there who are thinking about shooting down drones while they’re making deliveries, Amazon has a patented plan to stop you.
The patent, filed in 2014 but published just last week, lays out countermeasures for potential threats ranging from computer hacking to lightning flashes to bows and arrows.
If nothing else, the 33-page application illustrates how many things could possibly go wrong with an autonomous navigation system for unmanned aerial vehicles, or UAVs.
The “compromise system” that Amazon’s engineers propose relies on an array of sensors to orient the drone based on the sun’s position in the sky, if need be. That’s in case the drone gets confused by, say, lightning or a muzzle flash. Cont'd...
Records 1 to 11 of 11
Featured Product
NVIDIA RTX PRO BLACKWELL DESKTOP GPUs
NVIDIA RTX PRO - Built for Professionals - NVIDIA RTX PRO Blackwell Desktop GPUs feature the latest breakthroughs in AI, ray tracing, and neural rendering technology to power the most innovative workflows in design, engineering, and beyond.
Robotics and Automation - Featured Company

Electrocraft Inc.
ElectroCraft, Inc. is a global provider of dependable, application-engineered fractional-horsepower motor and motion products. Our products are found in thousands of different applications within industrial, commercial, and consumer product markets. While ElectroCraft provides a wide array of standard products with many configurable options, we have built our brand on custom OEM solutions that meet the precise performance, cost and quality our customers require.